DATA PROTECTION ADDENDUM
Customer has entered into a Master Agreement or into an agreement with similar nature and purpose (hereinafter “Master Agreement”) with G-P. The execution of such Master Agreement may entail the Processing of Personal Data. The Customer and G-P (jointly referred to as “Parties”) agree that this Data Protection Addendum (“DPA”) sets forth their obligations with respect to the processing and security of Personal Data in connection with the Services provided by G-P to the Customer under the Master Agreement and the Parties agree to be bound by this DPA. This DPA supplements the terms and conditions in the Master Agreement and is incorporated therein. In the event of a conflict between this DPA, and any other agreement between the parties on the issues set forth herein, this DPA shall prevail. If Customer already has an executed data protection addendum in effect with G-P, then that agreement shall prevail over this DPA, and this DPA shall have no force or effect, unless otherwise agreed in writing by Customer and G-P.
Whereas:
- When G-P provides the Customer with Employer of Records (“EOR”) services, G-P assumes the role of the legal employer for any individuals selected by the Customer (“Professionals”) to be hired.
- With regard to such Professionals' Personal Data, G-P is a Controller during the course of the employment relationship.
- With regards to Professionals' Personal Data collected and used by the Customer for its own purposes, Customer is also a Controller with independent privacy obligations.
- When delivering the EOR services, the exchange of Professionals' Personal Data between G-P and the Customer is under an independent Controller-to-Controller relationship and the Controller-to-Controller terms defined in section 2 below, shall apply.
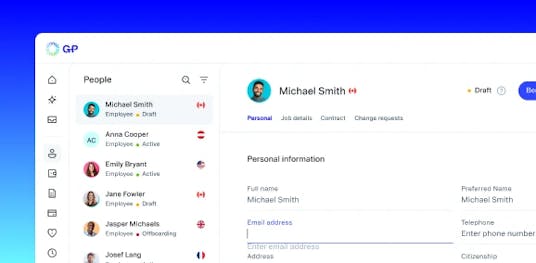
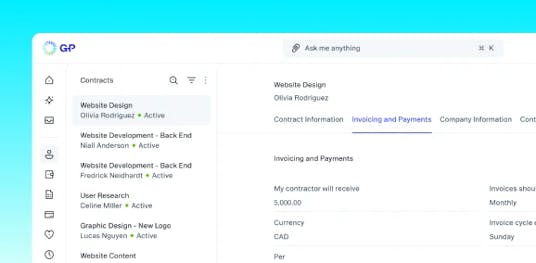
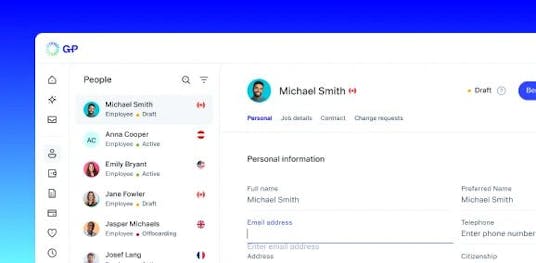
- G-P also offers various software as a service products via G-P’s platform (“GPP”), through which G-P enables Customer to manage the relationship with those Professionals.
- By providing Customer with access to GPP, G-P is the Processor for the account related data uploaded to the GPP by the Customer's appointed Authorized Users of GPP and the Controller-to-Processor terms defined in section 3 bellow, shall apply.
G-P and the Customer has agreed as following:
1. DEFINITIONS
1.1. Terms not defined herein have the meanings set forth in the Master Agreement. The following words in this DPA have the following meanings:
1.2. “Authorized User” means an individual permitted by Customer who may include either or a Customer’s employee and/or contractor, to access and use the GPP on behalf of the Customer, pursuant the execution of the Master Agreement.
1.3. “Customer Data” means any Personal Data related to any Authorized User or identifiable natural person that is transferred, processed, or stored by G-P on behalf of Customer for the use of the GPP by the Customer.
1.4. “Data Protection Laws” means any data protection and privacy laws to which a party to this Agreement is subject and which are applicable to the Services provided, including where applicable, but not limited to, GDPR, UK GDPR, Swiss Data Protection Laws, US Privacy Laws (including state and federal laws), and Brazil LGPD.
1.5. “GDPR” means the General Data Protection Regulation (EU) 2016/679.
1.6. “GPP” means G-P’ proprietary software, including without limitation, the software, the mobile version, any software contained therein, and any data made available through the use of either G-P’ proprietary software or the third party services, including their updates, upgrades, platform as a service and, documentation.
1.7. “EEA” means the European Economic Area.
1.8. “LGPD” means Brazil Law No. 13.709, the General Law on Protection of Personal Data, as may be amended, superseded, or replaced.
1.9. “Master Agreement” means the agreement executed between Customer and G-P for the provision of the Services.
1.10. “Privacy Policy” means G-P´s privacy policy, as updated from time to time, available at https://www.globalization-partners.com/privacy-policy/
1.11. “Professionals´ Data” means Professionals´ Personal Data processed by G-P in the course of its EOR services provision to Customer.
1.12. "Restricted Transfer" means any transfer of Personal Data to a country outside the EEA, the United Kingdom, Switzerland or Brazil that is not subject to an adequacy decision under the applicable Data protection Laws, and therefore requires appropriate safeguards under applicable data protection laws.
1.13. “Services” mean the services to be provided by G-P to the Customer under the Master Agreement which may include the EOR services and the access and use of GPP.
1.14. "Standard Contractual Clauses" or "SCCs" mean (i) where the GDPR applies, the standard contractual clauses annexed to the European Commission's Implementing Decision (EU) 2021/914 of 4 มิถุนายน 2021 standard contractual clauses for the transfer of personal data to third countries pursuant to Regulation (EU) 2016/679 of the European Parliament and of the Council, available at https://eur-lex.europa.eu/legal-content/EN/TXT/HTML/?uri=CELEX:32021D0914&from=EN ("EU SCCs"); (ii) where the UK GDPR applies, the applicable standard data protection clauses adopted pursuant to Article 46(2)(c), or (d) where the UK GDPR means the International Data Transfer Addendum (“UK Addendum”) to the EU Standard Contractual Clauses issued by the Information Commissioner's Office under s.119A(1) of the Data Protection Act 2018, as such UK Addendum may be revised under Section 18 therein ("UK SCCs"); (iii) where the Swiss Data Protection Laws apply, the applicable standard data protection clauses issued, approved or recognized by the Swiss Federal Data Protection Authority and Information Commissioner´s Office (the "Swiss SCCs); where the Brazilian LGPD applies, the applicable standard contractual clauses, attached to Resolution CD/ANPD No. 19/2024 promulgated by the Brazilian National Data Protection Authority (“ANPD”), as they may be amended from time to time (“Brazil SCCs”).
1.15. “Swiss Data Protection Laws” or “FADP” means (i) Swiss Federal Data Protection Act (dated มิถุนายน 19, 1992, as of 1 มีนาคม, 2019) (“FDPA”); (ii) The Ordinance on the Federal Act on Data Protection (“FODP“); and (iii) any national data protection laws made under, pursuant to, replacing or succeeding and any legislation replacing or updating any of the foregoing.
1.16. “UK Addendum” means the United Kingdom international data transfer addendum to the EU Standard Contractual Clauses issued by the UK Information Commissioner.
1.17. “UK Data Protection Laws” mean the GDPR as saved into United Kingdom law by virtue of section 3 of the United Kingdom's European Union (Withdrawal) Act 2019 ("UK GDPR") and the Data Protection Act 2018 (together, "UK Data Protection Laws").
1.18. “US Privacy Laws” means applicable United States (US) state laws, orders, regulations and regulatory guidance relating to the Processing of Personal Data including without limitation: (a) the CCPA; (b) Virginia’s Consumer Data Protection Act; (c) the Colorado Privacy Act; (d) Connecticut’s Act Concerning Data Privacy and Online Monitoring; (e) the Utah Consumer Privacy Act; and (f) all similar state laws
1.19. "Controller" "Data Subject", "Personal Data", “Personal Information” “Data Breach”, "Processor", "Process/Processing", “Restricted Transfer”, “Service Provider” and/or any other similar terms and concepts shall have the meanings as defined in Data Protection Laws.
2. CONTROL OF PERSONAL DATA
2.1. Roles of the Parties. Where G-P operates as an independent Controller, G-P shall comply with its Controller obligations under Data Protection Laws when Processing Personal Data and shall Process the Personal Data as described in G-P’s Privacy Policy available at https://www.globalization-partners.com/privacy-policy/. ลูกค้าจะต้องปฏิบัติตามข้อผูกพันของตนภายใต้กฎหมายคุ้มครองข้อมูลเมื่อประมวลผลข้อมูลส่วนบุคคลในฐานะผู้ควบคุม In no event will the Parties Process Personal Data under this DPA as joint Controllers.
2.2. Responsibilities and Acknowledgements. Each Party may process Personal Data under this DPA with respect to Professionals’ Data as independent data Controllers. The Parties agree to comply with their respective obligations and to process any Personal Data fairly and lawfully in compliance with this DPA and all Data Protection Laws applicable to such Party’s Personal Data Processing operations. Each Party shall ensure that its Processing of Personal Data is limited to the purpose of the GPP provided by G-P and is based on a legal ground for lawful processing. The Parties will assist each other in complying with their respective obligations under Data Protection Laws, including, but not limited to, assisting each other if a Data Breach occurs, responding to Data Subjects and/or regulators’ requests.